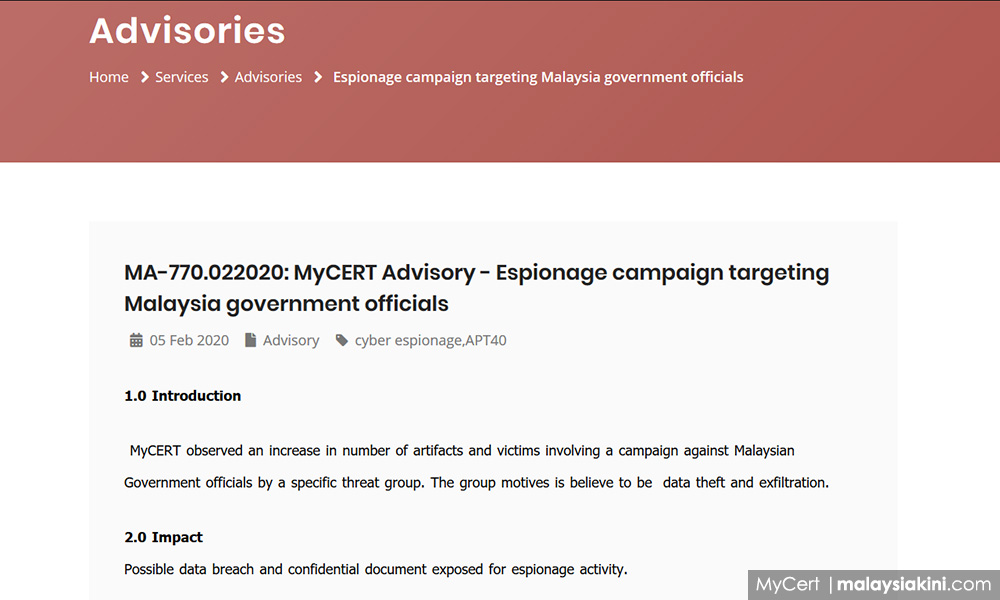
The Malaysia Computer Emergency Response Team (MyCert) has warned of a cyberespionage campaign targeting government officials.
While its security advisory referred to the hackers only as a “specific threat group”, the document hinted at the group APT40 — a cyber-espionage group that security researchers believe are working for the Chinese government.
The MyCert advisory is tagged “APT40”, and it referenced four documents in its footnotes that describe APT40’s tools and modus operandi.
According to the technology news website ZDNet, APT40’s hacking activities is known to be aligned with interests of the Chinese government, especially when it comes to “engineering, transportation, and the defence industry, especially where these sectors overlap with maritime technologies”.
It quoted a group of cyber-security analysts claiming that APT40 are hired contractors and are operating under the supervision of the Chinese Ministry of State Security’s Hainan Department.
Meanwhile, MyCert’s advisory on Wednesday said the hackers aimed to steal data on government-backed projects.
“The group's operations tend to target government-sponsored projects and take large amounts of information specific to such projects, including proposals, meetings, financial data, shipping information, plans and drawings, and raw data,” it said.
MyCert is a government agency under Cybersecurity Malaysia and is under the purview of the Multimedia and Communications Ministry.
It did not say whether the hacking attempts were successful.
To make the hacking attempt, MyCert said the group first sent “spear-phishing” emails to their victims. This was done either through email addresses that had already been previously compromised or through impersonation.
Spear-phishing is a form of cyberattack that relies on deception to trick victims into revealing sensitive information or to perform a particular action, such as to open a malicious file.
In this case, MyCert said the hackers masqueraded to be journalists, representatives from trade publications, or someone from a relevant military organisation or NGO.
They sought to coax their victims into opening an infected Microsoft Office document, which is either sent to the victim as an email attachment or Google Drive link.
Once the file is opened, it triggers the download and execution of malicious software.
MyCert urged computer users to keep their software up-to-date and follow their organisation’s security best-practices.
“Generally, MyCert advises the users of this devices to be updated with the latest security announcements by the vendor and follow best practices on security policies to determine which updates should be applied,” it said.

